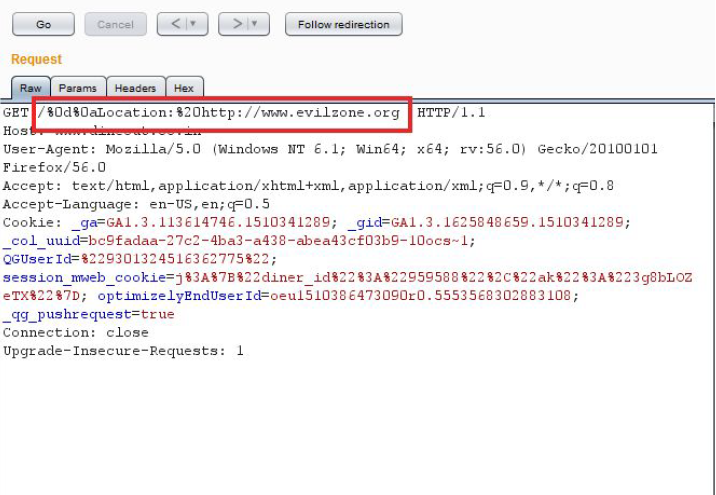
BugBounty — Exploiting CRLF Injection can lands into a nice bounty | by Avinash Jain (@logicbomb) | InfoSec Write-ups
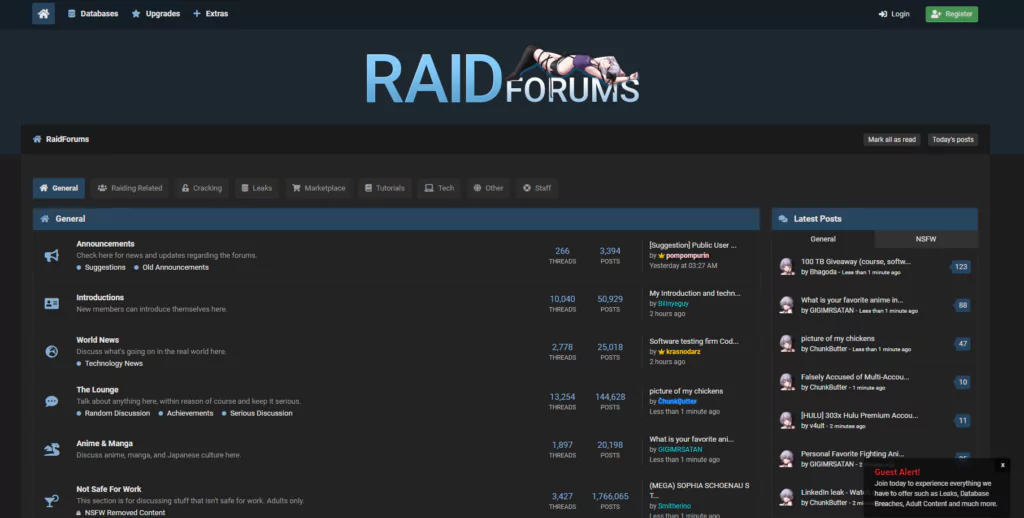
Top 5 Underground Hacker Forums That are Accessible via Your Web Browsers such as Google Chrome, Firefox, and Internet Explorer - SOCRadar® Cyber Intelligence Inc.

















/presentations/hacking/en/slides/sl29-1515983462372.jpg)
